Created on Friday, 18 July 2014 18:07
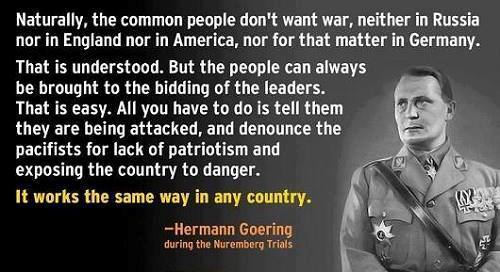
Throughout history, versions of the false flag attack have been used successfully by governments in order to direct the force of the people toward whatever end the so-called "powers that be" may be seeking. At times, that end may be war, or it may be the curtailing of domestic civil liberties and basic human rights. In others, it is an economic agenda.
Indeed, false flags are themselves capable of taking on a wide variety of forms – domestic or foreign, small or large, economic or political, and many other designations that can often blur into one another. Each may serve a specific purpose and each may be adjusted and tailored for that specific purpose as societal conditions require.
For instance, the chemical weapons attack which took place inside Syria in August 2013 serves as an example of a foreign false flag designed to whip up American fervor for war, on the platform of 'Responsibility to Protect', similar to the Gulf of Tonkin.
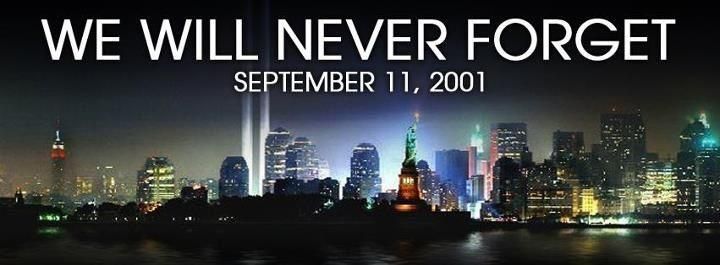
Domestically speaking (USA), a large-scale false flag such as 9/11, can be used to whip up both massive public support for war and a popular willingness to surrender civil liberties, constitutional procedure, and constitutional/human rights. Economic false flags may take the form of manufactured “government shutdowns” or “government defaults” designed to create a demand for austerity or other pro-Wall Street solutions. Lastly, smaller-scale domestic false flags such as Sandy Hook or Aurora, often involve the implementation of gun-control measures or a greater police state.
There are, of course, many different versions of false flag attacks and none fit into a tightly crafted classification beyond the generalized term “false flag.” As stated above, some false flags may indeed embrace an element of each of the different versions listed previously both in terms of methodology and purpose.
With that in mind, it is also true that, while massive false flag attacks are always a possibility, it has been the small-scale false flags coming in the form of “shooters” (most often of the “lone gunmen” variety), that have been used most effectively by the ruling class and its mouthpiece media outlets in recent years. While the scale of the attacks has diminished, their frequency has rapidly increased.
However, due to a growing competent alternative media and researching community, as fast as the false flag attacks are launched, a volley of deconstructions of the official narratives are being provided. While many criticisms of the official version of events are wildly incredible, bordering on paranoia and impossibility, there are capable outlets and researchers who are able to expose the false flag for what it is. Indeed, it is for this reason that the false flag has suffered serious setbacks in terms of its effectiveness as of late and why it continues to do so.
Because the false flag attack is designed to instill fear, panic, and a guided response from the general public, it is important to deconstruct the narrative of that attack as it is presented. However, we cannot simply be consumed by attempting to expose and deconstruct every false flag attack that comes our way. We cannot ignore the greater issues, the winnable battles, and the demands we must be making simply to expose each and every false flag. We cannot ignore the forest fire to extinguish the occasional burning bush. The false flag, after all, is only the symptom of the disease. For that reason, it is important to enable the general public to recognize the false flag event when it happens – thus rendering the attack neutral – and not simply the questionable elements of a particular false flag which will soon be overtaken by a new one.

The following is a list of some of the most common elements of a false flag attack, which should immediately be looked at in the event of an incident that pulls at the heartstrings and emotions of the general public.
1. High Profile Event: The first question to ask would be “Is this a high profile incident?” The answer, of course, is fairly obvious. If an attack takes place at the World Trade Center complex causing the buildings to explode and collapse, or if it takes place at the White House, or Pentagon, it is clearly high profile. Thus, the location can be factored in. In other circumstances, however, the act itself may be the major factor such as the case in Sandy Hook Elementary School, a nationally unimportant location but a horrific act that made national news nonetheless. The most important factor, of course, is media attention. Regardless of location or the act, if the media picks up the story and runs it simultaneously on all major mainstream channels, the incident can be considered a “high profile event.”
2. Changing Stories: In informed researching circles, it is well-known that the information that comes out shortly after the event is usually the most reliable. This is not to discount the existence of confusion related to panicked reports coming from eyewitnesses and the like. However, the information coming out early on has not yet been subjected to the top-down media revision that will inevitably take place as the story becomes molded to fit the narrative pushed by the individuals who either directed the attack at the higher levels or at least have connections with those who are able to control the manner in which various media outlets report the event.
For instance, in times of false flag attacks, the initial reports may point to 5 gunmen. Very shortly after, reports may only mention two. Only a few hours after the attack, however, all references to more than one gunmen are removed entirely, with only the “lone gunman” story remaining. Any other mention of additional gunmen after this point is ridiculed as “conspiracy theory.”
3. Simultaneous Drills: Sometimes a false flag operation can be identified by the running of drills shortly before or during the actual attack. Many times, these drills will involve the actual sequence of events that takes place during the real-life attack. These drills have been present on large scale false flags such as 9/11 as well as smaller-scale attacks like the Aurora shooting.
For instance, as Webster Tarpley documents in his book 9/11 Synthetic Terror: Made In USA, at least 46 drills were underway in the months leading up to 9/11 and on the morning of the attack. These 46 drills were all directly related to the events which took place on 9/11 in some way or another. Likewise, the 7/7 bombings in London were running drills of exactly the same scenario that was occurring at exactly the same times and locations.
Although one reason may take precedence over the other depending on the nature and purpose of the operation drills are used by false flag operators for at least two reasons. One such purpose is the creation of intentional confusion if the drill is taking place during the actual attack. The other, more effective aspect, however, is using the drill as a cloak to plan the attack or even “go live” when it comes time to launch the event. Even more so, it gives the individuals who are involved in the planning of the event an element of cover, especially with the military/intelligence agency’s tight chain of command structure and need-to-know basis. If a loyal military officer or intelligence agent stumbles upon the planning of the attack, that individual can always be told that what he has witnessed is nothing more than the planning of a training exercise. This deniability continues all the way through to the actual “going live” of the drill. After the completion of the false flag attack, Coincidence Theory is used to explain away the tragic results.
4. Cui Bono? The most important question to ask immediately after any high profile incident is “cui bono?” or “Who benefits?” If one is able to see a clear benefit to any government, corporation, or bank, then the observer becomes capable of seeing through the false flag attack immediately. Many of these questions can be answered by taking a closer look at the behavior of these organizations prior to the attack and shortly thereafter.
For instance, the presence of legislation that would stand little chance of being passed before the attack, but which is quickly passed and/or heavily pushed afterward is one clue that the conveniently timed 'attack' was actually a government-orchestrated false flag operation.
Patriot Act style legislation was actually written before 9/11 but stood little chance of passing in Congress due to the political climate in the United States at the time. After 9/11, however, the Patriot Act was fast-tracked through both Houses of Congress with virtually no debate and with the blessing of the American people.
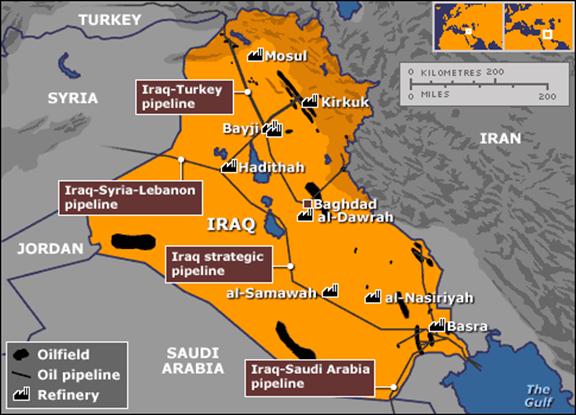
Returning to 9/11, it is a fact that a number of individuals who were in positions of power within the US government during the time the attack occurred had desperately wanted to invade several Middle Eastern countries. After the attacks, a war psychosis gripped the ruling class of the United States and the American public followed right along.
After the Underwear Bombing, we saw the rollout of the TSA full-body scanners, a technology that would not have been readily accepted prior to the incident and subsequent propaganda campaign. However, the scanners had been purchased one year earlier by a firm owned by Michael Chertoff, the former head of Homeland Security.
Likewise, in terms of the LAX shooting, TSA purchased 3.5 million dollars worth of ammunition in August. Yet, in August, TSA was not an armed agency. After the LAX shooting, however, talk has turned to arming the agency, thus indicating possible foreknowledge on the part of someone higher up in the governmental structure.
Of course, the same can be said for the explosion of crazed lone-gunman shooting sprees that took place all across the United States amid propaganda pushes for increased gun control measures.
5. Unanswered Questions: Another hallmark of the false flag operation is relatively obvious – the presence of unanswered questions regarding the details of the attack, the perpetrators, the motive and so on. Although the media narrative that takes shape soon after the attack will ignore these questions, they will inevitably remain if observers are able to think for themselves and focus only on the information. An example of such questions would be Building 7 on 9/11 or the questions of additional shooters at Aurora and Sandy Hook.
6. Case is quickly closed: Once an acceptable patsy and cover story is chosen by the media, all other opinions and questions are refused air time. Nothing that even slightly contradicts the official story is acknowledged as legitimate. Once this happens, the patsy, if still alive (in rare circumstances) is charged, prosecuted, and convicted in a largely secret or shadowy proceeding. In most cases, the suspect is killed in the process or shortly after the fact thus negating any first-hand contradiction of the official narrative. Either way, the case is closed very soon after the event.
7. Suspects’ Connection to CIA, FBI, or Other Intelligence Agencies: One key aspect suggesting a false flag that should be looked for soon after the attack is any possible connection the suspect or group of suspects may have had with intelligence agencies. A connection to any one of these organizations and institutions may go some length in explaining how the attack was coordinated, the motivation of the perpetrators, the actual involvement (or not) of the suspects, and who actually directed the operation. For instance, on 9/11, many of the alleged hijackers had previously had close contact with the FBI, CIA, and other high-level intelligence agencies (both home and abroad).[5] Likewise, the Tsarnaev brothers who have been accused of masterminding and carrying out the Boston Bombing had ties to the FBI before the attack.
In many instances, connections to certain military agencies and communities should serve as the same red flag as connections to intelligence agencies since these institutions have largely been blended together.
8. Convenient Scapegoat: One clue leading an informed observer to suspect a false flag attack is the existence of the convenient scapegoat. Any false flag operation will have a carefully crafted narrative complete with a group of individuals set up for demonization. The OKC bombing had McVeigh and thus, “right-wing extremists” and “militias.” On 9/11, the group was Muslims. In many of the domestic shooting sprees, the demonization was set for gun owners. With the recent LAX shooting, the “perpetrator” was an “anti-government conspiracy theorist.” In the instance of the false flag, a readily identified pasty will exhibit all or most of the aspects of the group and social demographic set to be demonized.
9. Media Promotes A Narrative Against Scapegoat Groups and/or An Agenda To Take Liberties: One clue suggesting a false flag is that, immediately after the attack and after the perpetrators have been “identified” by “officials” and the corporate media outlets begin not only demonizing the demographic group to which the “perpetrator” belongs, but begins promoting “solutions” in order to prevent such an attack from ever happening again. This narrative will always involve the erosion of liberties, the greater implementation of a police state, a specific economic policy, or a march to war.
Simply put, the media promotes the PROBLEM, allows for and guides the REACTION, and then provides the pre-determined SOLUTION.
10. Government Begins to “Take Action” Against the Scapegoat or Moves Along the Lines of the Media Narrative: After a healthy dose of propaganda from mainstream media
Conclusion:
Although it is extremely important to educate the general public as to the nature and purpose of false flags, education cannot be a goal in and of itself. The public not only needs to know the truth surrounding specific false flag events as they appear, but they also need to understand the methodology of identifying them on their own and in real-time.
Edited from: Activistpost.com
Related
The Business of War: How Federal And Private Military Contractors Profit From War